My Competencies
With over 20 years of practical hands-on experience from both an Operations and Business standpoint. I have had the privilege of learning from some of the best people in the industry. Thus becoming a named Subject Matter Expert (SME) in a few technologies that are redefining the direction of Cybersecurity.
Security Information and Event Management (SIEM)
Security information and event management (SIEM) technology supports threat detection, compliance and security incident management through the collection and analysis (both near real time and historical) of security events, as well as a wide variety of other event and contextual data sources. The core capabilities are a broad scope of log event collection and management, the ability to analyze log events and other data across disparate sources, and operational capabilities (such as incident management, dashboards and reporting).
Security Orchestration, Automations, and Response (SOAR)
Security information and event management (SIEM) technology supports threat detection, compliance, and security incident management through the collection and analysis (both near real-time and historical) of security events, as well as a wide variety of other event and contextual data sources. The core capabilities are a broad scope of log event collection and management, the ability to analyze log events and other data across disparate sources, and operational capabilities (such as incident management, dashboards, and reporting).
Managed Detection and Response (MDR)
Managed detection and response (MDR) services are a collection of network-, host- and endpoint-based cybersecurity technologies that a third-party provider manages for a client organization. The provider typically installs technology on-premises at the client organization and provides additional external and automated threat hunting services.
MDRs improve cybersecurity by searching for threats and responding to them once detected. They also let users connect with the provider’s security experts, who can bolster the security skills of the client company’s IT department. This makes them ideal for businesses that don’t have a designated in-house threat detection team.
Extended Detection and Response (XDR)
XDR, or Extended Detection and Response, represents an integrated suite of security tools designed to provide unified protection against cyber threats. This proactive approach seeks to detect, analyze, and respond to potential threats in real-time, covering the network, cloud, endpoint, and email security domains.
Threat Management (TM)
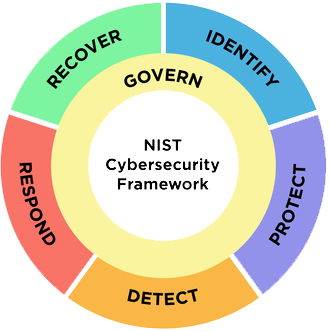
Threat management is a process used by cybersecurity professionals to prevent cyberattacks, detect cyber threats, and respond to security incidents. Why is threat management critical?
Most security teams face information fragmentation, leading to blind spots in security operations.
Next Gen Firewall (NGFW/UTM)

A next-generation firewall (NGFW) is part of the third generation of firewall technology that can be implemented in hardware or software. It can detect and block sophisticated attacks by enforcing security policies at the application, port, and protocol levels.
Cloud Computing (The Cloud)
Cloud computing is the on-demand availability of computer system resources, especially data storage and computing power, without direct active management by the user. Large clouds often have functions distributed over multiple locations, each of which is a data center.