Executive Case Study
In mid-2021, I was asked to rescue a stalled Managed Threat Detection and Response (MTDR) deployment at Tulane University, a $3M+ AT&T Cybersecurity engagement. Six months after contract signing, the deployment had stalled, the CIO was frustrated, and no progress was visible despite daily log submissions. I was given no budget, no timeline, and one directive: fix it.
Challenges Identified
- Sensor Overload – Palo Alto PA7050 Firewall logs exceeded sensor ingestion capacity, causing repeated crashes.
- Control Node Overutilization – Overload cascaded upstream, slowing processing and leaving the control node non-responsive.
- Delayed Threat Model Workshop (TMW) – Contractual holdups had stalled this critical step, leaving deployment improperly scoped.
Resolution Approach
- Conducted a deep-dive discovery with university IT to pinpoint log ingestion bottlenecks.
- Re-engineered log parsing and filtering at the sensor level to balance throughput.
- Coordinated with engineering and the customer to optimize resource allocation on the control node.
- Personally facilitated the long-delayed Threat Model Workshop, aligning stakeholders and clearing contractual obstacles.
Outcome
- Restored the control node to full functionality, stabilizing log ingestion.
- Regained trust with Tulane’s CIO through transparent communication and proactive remediation.
- Kept the project within the original budget, fulfilling the “no additional expenditure” mandate.
- Created a repeatable remediation framework later applied to other MTDR accounts.


Conclusion.
The Solution
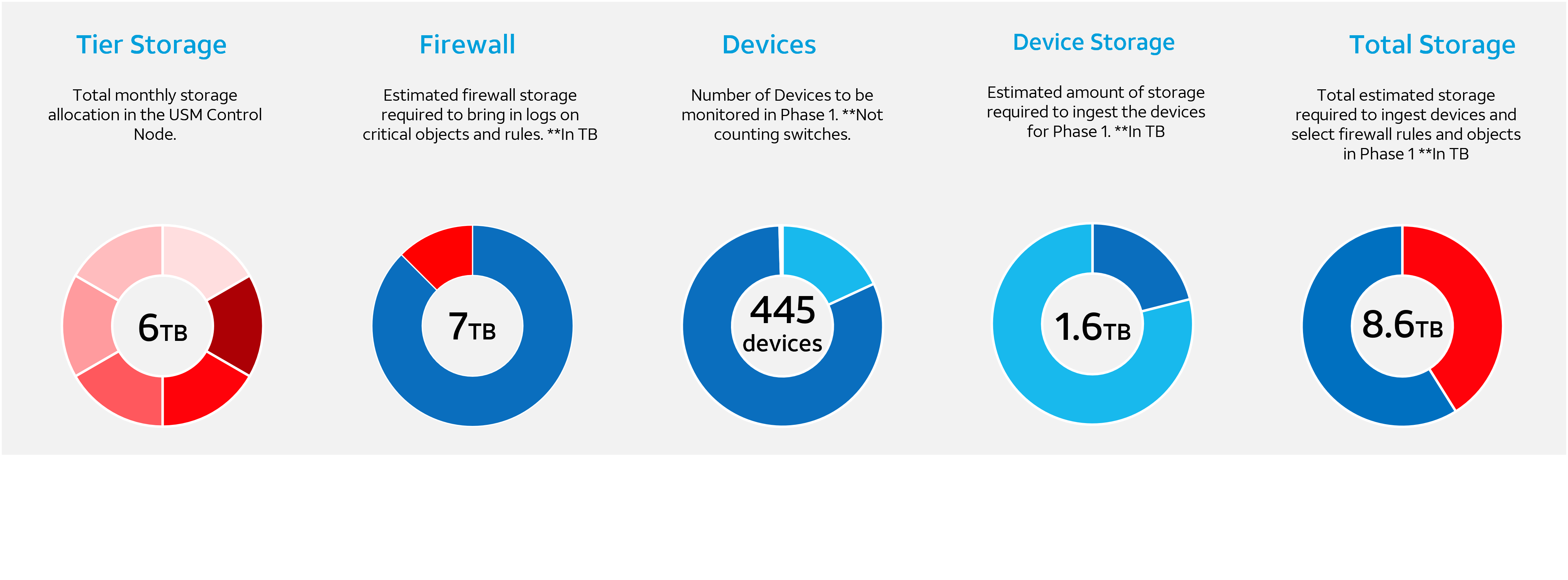
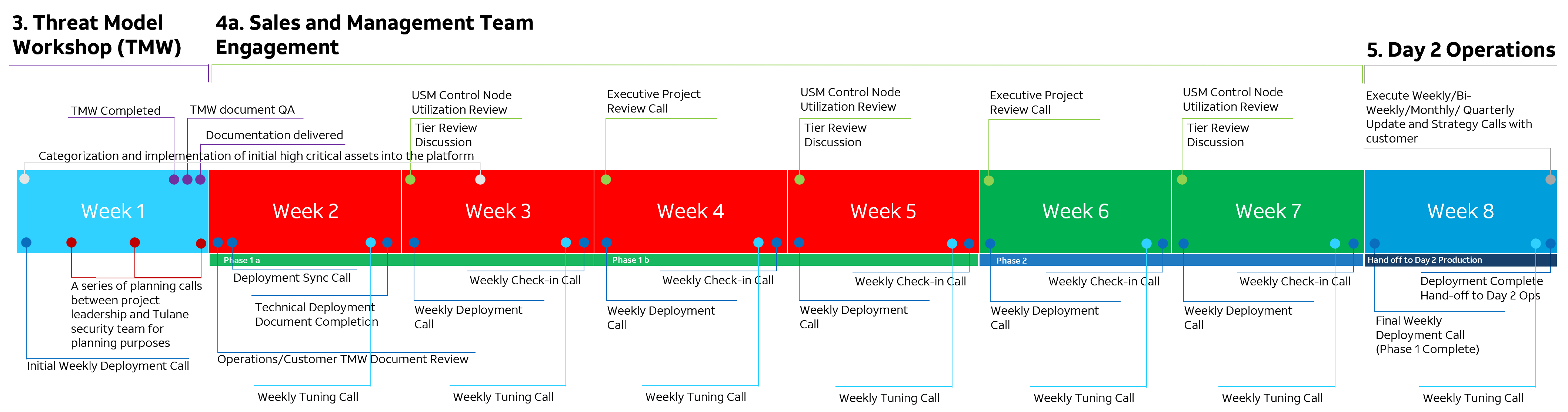
After facilitating the Threat Model Workshop, I worked with Tulane’s deployment team and security engineers to realign the MTDR deployment around business-critical assets. We broke the rollout into phases, prioritizing the most mission-critical systems first.
- Firewall Optimization: Partnered with Tulane’s firewall engineers to segment PA7050 logs by type and subnet, eliminating noise and stabilizing the control node.
- Phased Migration: Brought critical servers, load balancers, and switches online, ensuring visibility into the most essential traffic.
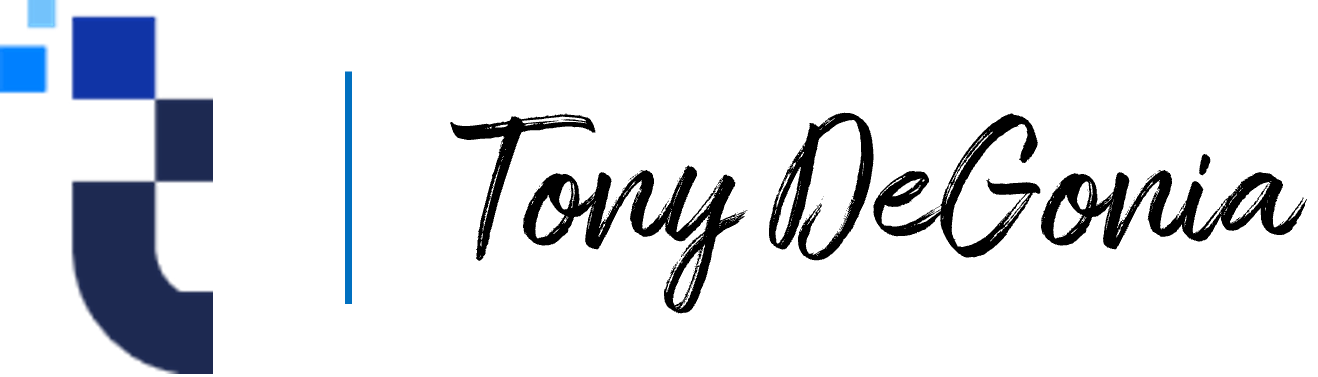
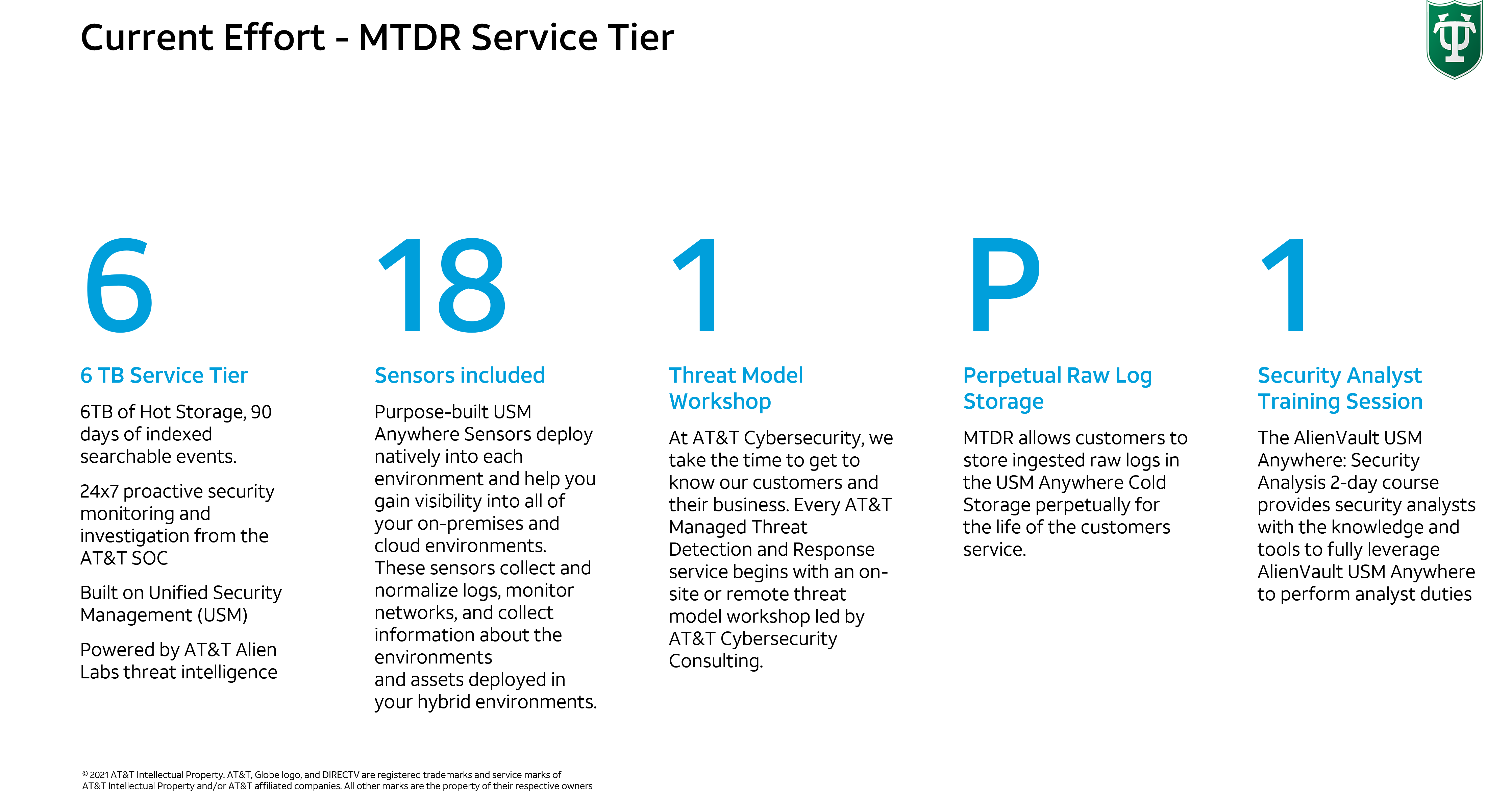
- Capacity Management: Surpassing 90% utilization of contracted storage highlighted the value of insights being generated. I guided Tulane through a storage upgrade from 6TB to 20TB/month, ensuring scalability.
- Completion & Visibility: With contractual updates finalized, the deployment team onboarded the remaining assets. By project close, Tulane had achieved 85% network/server/endpoint visibility, a significant uplift in security posture.
Impact
- Stabilized a previously stalled $3M MTDR deployment.
- Elevated Tulane’s SOC visibility from near-zero to ~85%.
- Drove incremental revenue by facilitating a 3x storage expansion (6TB → 20TB).
- Restored customer confidence and salvaged a high-risk account.
Results.
Increase in instance size
0
+%
weeks to bring customer to resolution
0
TCV of uplift at project conclusion.
$
0
K